Blockchain Security
:Wallet Attacks, Protocol Vulnerabilities, and Audit Gaps
Imagine waking up one morning to find all the assets in your crypto wallet gone. Was the cause a simple phishing trap where you handed over your recovery code (seed phrase), or did attackers exploit a vulnerability in the blockchain to manipulate the network? No matter how secure blockchain may appear on the surface, it actually harbors many threats. In this article, we focus on what we see as the three major dangers on the security front of the crypto universe:
Wallet attacks targeting users
Layer-1 protocol vulnerabilities at the heart of blockchains
Regulatory and audit gaps in decentralized systems
Seed Theft, Phishing, and Malicious Applications
Malware and phishing sites target crypto users’ wallets to steal their seed phrases.
No matter how strong the cryptography behind blockchain is, the weakest link is often the user. Attackers aim directly at wallets to seize crypto assets. Various attack methods have been developed at every level, from offline wallets to mobile apps.
Phishing Attacks: Fake websites or emails trick users into sharing their recovery phrases (seed phrases) or private keys. For example, scammers set up websites imitating official wallet interfaces or send messages like “your account is locked, enter these 12 words to unlock it.” In 2023, more than 324,000 crypto users fell victim to such scams, with total losses reaching about $295 million. Popular “wallet drainer” groups (e.g., Monkey Drainer, Inferno Drainer) caused tens of millions of dollars in losses before shutting down, only to be replaced immediately by new ones.
Malicious Applications and Extensions: A seemingly harmless mobile app or browser extension may steal wallet data in the background. Recently, Kaspersky researchers uncovered a spyware campaign called SparkKitty. This malware infiltrated the official Google Play and Apple App Store, infecting apps targeting crypto users. SparkKitty collected screenshots on devices, extracted seed phrases via optical character recognition (OCR), and transmitted them to attackers.
Recovery phrases stored as screenshots on phones were thus exposed. Similarly, fake crypto wallet extensions for browsers pose serious threats. For example, in the Lazarus group’s BlueNoroff operation, attackers targeted victims’ computers with a fake MetaMask extension. Through this method, all crypto transactions could be monitored and redirected; even transactions by hardware wallet users were manipulated.
Trojanized Hardware Wallets: Hardware wallets are usually considered among the safest methods, but a supply-chain vulnerability can have severe consequences. In one case, a supposedly “new” hardware wallet purchased online was found to contain pre-programmed private keys and backdoors. While the user could see funds in the wallet, attackers could remotely withdraw assets using those keys.
Attacks on Popular Wallets: Sometimes, the target is not individual users but entire wallet services. For example, in June 2023, Atomic Wallet users lost a total of $35 million in an attack carried out through an unknown method. When the stolen funds were traced to the Lazarus group, it was suspected that the attack may have involved distributing a fake version of Atomic Wallet or secretly injecting malicious code into the official app. This incident highlighted that users must not only take personal security precautions but also consider the reliability of the wallet apps they use.
Cyber attackers sometimes steal recovery phrases through simple phishing, and at other times infiltrate devices with advanced malware to access crypto assets. Therefore, basic precautions are critical for wallet security: never share seed phrases, only download apps and extensions from official sources, and obtain hardware wallets from trusted manufacturers.
Layer-1 Protocol Vulnerabilities and Double Spending
In the crypto world, the principle is: “once transactions are written to the blockchain, they cannot be changed.” This is one of the core promises of Bitcoin and similar systems. However, this rule can be broken if the majority of the network is taken over.
A 51% attack occurs when a majority of a blockchain’s consensus mechanism (e.g., mining power in proof-of-work systems like Bitcoin and Ethereum’s old model) is controlled by an attacker. If an attacker or group controls more than 51% of total mining power (or total stake in proof-of-stake systems), they can theoretically rewrite new blocks, invalidate some existing blocks, reverse their own transfers, and thus spend the same coins twice. They can also block transactions they dislike or bring the network to a halt. This severely undermines the trustworthiness of the blockchain.
History has seen such attacks. For example, in May 2018, Bitcoin Gold suffered an attack where about $18 million worth of BTG coins were double-spent. The Ethereum Classic (ETC) network also endured multiple 51% attacks over the years. In August 2020, ETC was attacked three times in a row, leading to about $9 million in double spending. In one of these attacks, more than 4,000 blocks were rolled back, and ETC deposited into exchanges was re-spent, causing losses to exchanges.
For large networks like Bitcoin, such an attack is theoretically possible but practically almost impossible due to the enormous computing power required—controlling the majority would demand astronomical costs and infrastructure. To date, Bitcoin and Ethereum’s main networks have never been successfully attacked in this way. However, smaller or newer networks with fewer miners or validators are more vulnerable. Moreover, cloud mining services make it possible for attackers to temporarily rent massive processing power to launch attacks.
A recent example occurred in 2025 when the Monero network, known for its privacy focus, experienced a notable incident. In August, a group called “Qubic” claimed to have seized 51% of Monero’s hash power after a month-long operation. During this period, a six-block reorganization occurred, invalidating the last 60 transaction blocks. Although Monero developers did not describe the event as a full 51% attack, the group openly stated that with such power, double spending or transaction censorship could be possible. This shows that even strong networks can be subject to coordinated attacks.
Protocol-level risks are not limited to malicious attacks. Software bugs can also create severe vulnerabilities. For example, a previously discovered bug in Bitcoin’s code (quickly patched) could have theoretically allowed the creation of an unlimited number of new Bitcoins. Some new blockchain projects have suffered outages due to insufficiently tested consensus algorithms. For instance, in 2022, the Solana network experienced a consensus error that halted block production for about seven hours. Although not an attack, this incident showed how a protocol flaw can bring an entire network to a standstill.
In conclusion, while the consensus mechanism underlying blockchains is innovative, it remains open to abuse and error. Smaller and newer networks are more vulnerable to 51% attacks and similar threats. Larger networks are more resilient, but not entirely immune. Developers must regularly audit and update protocol code, and users should be aware of these risks, especially with smaller projects.
Audit Gaps in the Blockchain World
The core philosophy of blockchain technology is to eliminate the need for central authorities and reduce intermediaries in the financial system. However, this also creates regulatory gaps and audit deficiencies. In traditional banking systems, government institutions, regulatory authorities, and insurance mechanisms provide certain safeguards. In the crypto ecosystem, where rules are not yet fully established, malicious actors find opportunities while investors are often left unprotected.
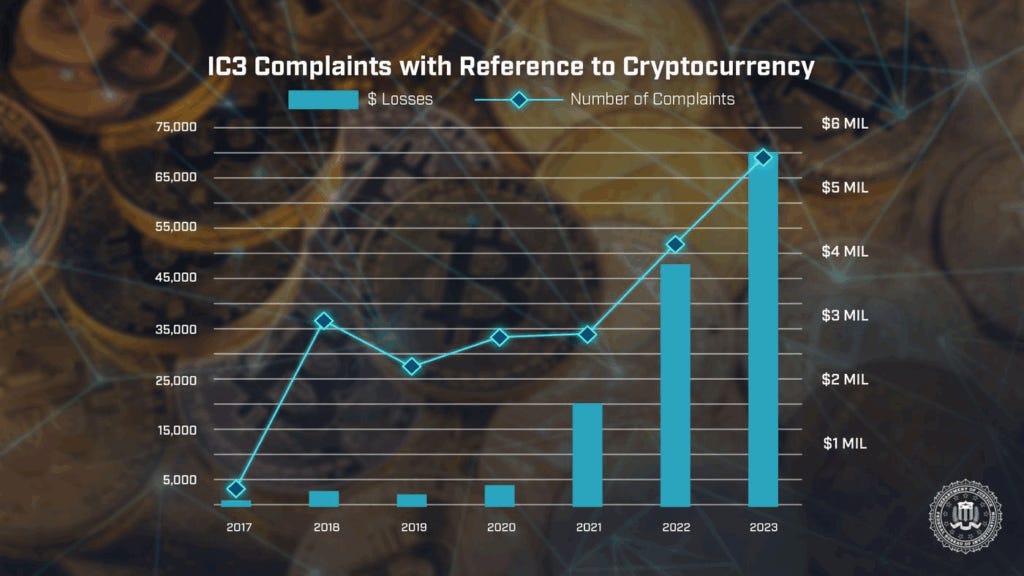
The weak legal frameworks and lack of centralized oversight in crypto provide users with anonymity and freedom but also convenience for criminals. Fraudsters and attackers exploit the irreversibility and pseudonymity of transactions. For instance, when a user is deceived by phishing, stolen assets can instantly be split across multiple accounts and exchanged on decentralized exchanges (DEXs) to obscure their trail. This process often takes just minutes, leaving the victim with no official authority to turn to. According to FBI data, crypto-related losses rose 45% year-on-year in 2023. Complaints about crypto fraud also hit a record high at 69,000.
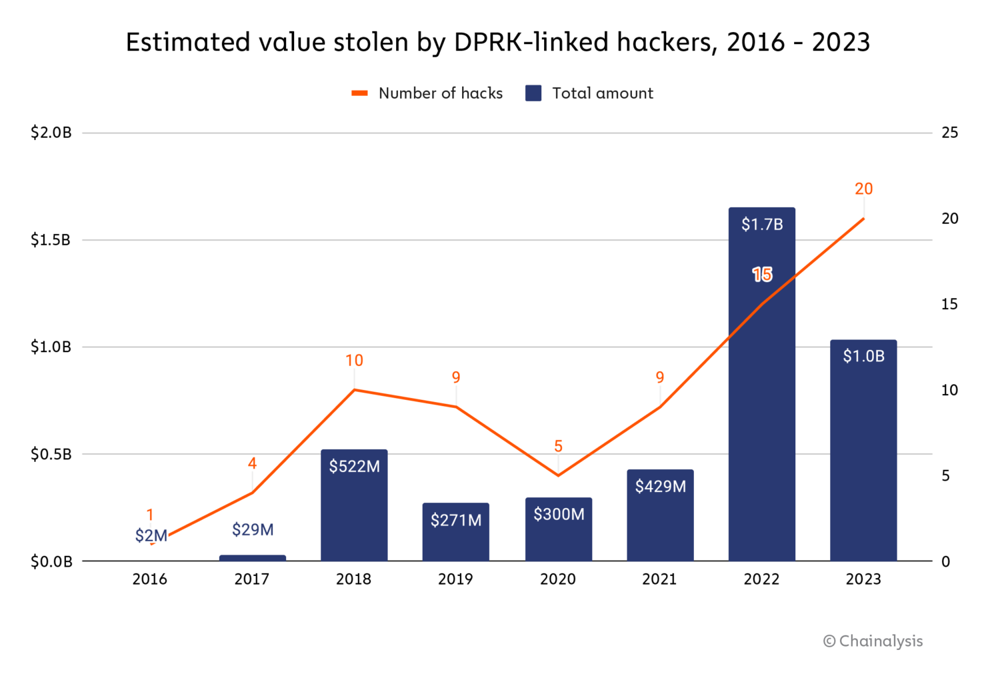
A similar lack of oversight exists in the decentralized finance (DeFi) ecosystem. Because DeFi protocols operate automatically through smart contracts, they are not managed by centralized companies. This creates accountability gaps. For example, if a critical software bug is exploited to steal billions in assets from a DeFi platform, there is no insurance or official authority to compensate users’ losses. In the first half of 2022 alone, over $1 billion worth of assets were stolen in DeFi protocol attacks, most attributed to North Korean groups. In such cases, victims often cannot find a legal counterpart.
The absence of a “lender of last resort” like governments or central banks, which intervene in traditional finance, further increases risks in the crypto market.
Globally, governments and regulators accelerated their actions following major fraud scandals and exchange collapses (such as the FTX collapse in 2022). In 2023, the European Union adopted MiCA, which took effect in 2025, requiring crypto service providers to meet licensing and transparency standards. In the U.S., while there is no comprehensive federal law, the SEC and CFTC intervene using existing laws. Internationally, the FATF is pushing for the application of KYC and AML standards.
Still, regulating decentralized structures is highly challenging. Questions remain unanswered, such as which legal system DAOs fall under or who bears responsibility for outcomes of smart contracts.
For blockchain to mature, a balanced approach is needed. Overly strict regulations stifle innovation, while excessive flexibility increases fraud risks. Thus, dialogue between the industry and regulators is critical. The goal should be to protect users while allowing room for technological growth.
Lessons to Be Learned
Blockchain and the crypto ecosystem have introduced major innovations to the financial system and continue to do so. However, this technology also carries its own vulnerabilities and threats. If wallet security, protocol weaknesses, and regulatory gaps are ignored, users and institutions may face serious risks.
Security responsibility must be shared across the ecosystem. Individual users must securely store seed phrases, only use official apps, and follow basic cyber hygiene practices. Developer teams must audit their code and benefit from open-source community reviews. Companies must implement insurance and transparent reserve practices to protect user funds.
For regulators, a balanced approach is also critical. Overly strict regulations can hinder innovation, while excessive flexibility raises fraud risks. International cooperation is needed to develop reasonable standards and reduce legal gaps.
Ultimately, security is not a product but an ongoing process. As threats evolve, all actors in the ecosystem must strengthen their defenses. The future of blockchain depends on how seriously this process is taken.